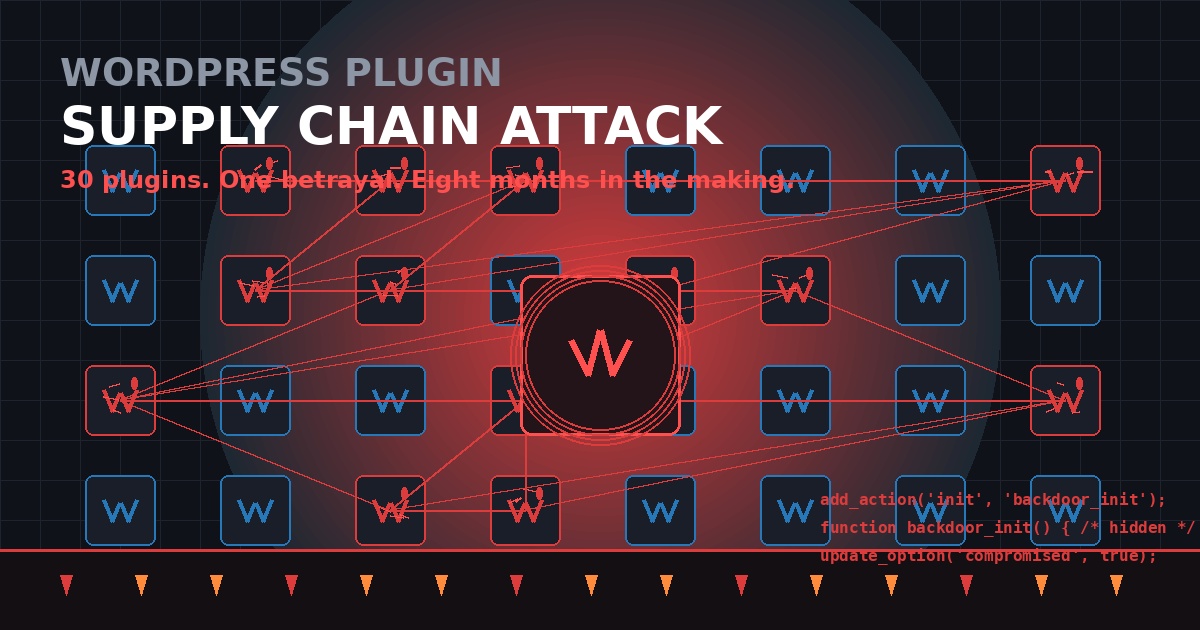
How 30 WordPress Plugins Were Weaponized Overnight
Last week, a single WordPress plugin called Countdown Timer Ultimate started showing security warnings in dashboards across the internet. The WordPress.org Plugins Team had flagged it: code inside could allow unauthorized third-party access.
That was just the first domino.
Within 48 hours, it became clear this wasn't an isolated incident. Thirty-one plugins from the same author had been permanently closed. Hundreds of thousands of sites were potentially compromised. And the attack had been planted eight months before it was ever activated.
This is the largest plugin portfolio supply-chain attack we've seen—and it followed a playbook that's happened before, just at a much larger scale.
What Happened
The story starts in 2015, when an India-based team began building WordPress plugins under the name "WP Online Support." Over the next decade, they grew a portfolio of 30+ free plugins with premium upgrades, rebranding as Essential Plugin in 2021.
By late 2024, revenue had declined 35–45%. The founders listed the entire business on Flippa, the online marketplace for buying and selling digital assets. A buyer identified only as "Kris"—with a background in SEO, crypto, and online gambling marketing—purchased everything for six figures. Flippa even published a case study about the sale in July 2025.
The buyer's very first SVN commit to the plugin repository was a backdoor.
Version 2.6.7, released August 8, 2025, added 191 lines of code disguised as a "WordPress 6.8.2 compatibility check." In reality, it introduced:
- A
fetch_ver_info()method that calledfile_get_contents()on an attacker-controlled server - A PHP deserialization backdoor allowing arbitrary function execution
- An unauthenticated REST API endpoint with
permission_callback: __return_true
The code sat dormant for eight months.
Then, on April 5–6, 2026, the backdoor was activated. The plugin's wpos-analytics module phoned home to analytics.essentialplugin.com, downloaded a backdoor file, and injected a massive block of PHP into wp-config.php. The injected code served SEO spam and redirects only to Googlebot, making it invisible to site owners.
Here's the most sophisticated part: the attacker resolved their command-and-control domain through an Ethereum smart contract, querying public blockchain RPC endpoints. Traditional domain takedowns wouldn't work—the attacker could update the smart contract to point to a new domain at any time.
The Response
On April 7, 2026, the WordPress.org Plugins Team closed all 31 plugins in a single day. On April 8, they forced an auto-update to version 2.6.9.1 across all installations, which commented out the backdoor line and added return; statements to disable the phone-home functions.
But here's the problem: the forced update did not clean wp-config.php. Sites that had already been compromised still had the malicious code injected into their configuration files, continuing to serve hidden spam to search engines.
Affected Plugins
All of the following plugins have been permanently closed and should be removed immediately:
- Accordion and Accordion Slider
- Album and Image Gallery Plus Lightbox
- Audio Player with Playlist Ultimate
- Blog Designer for Post and Widget
- Countdown Timer Ultimate
- Featured Post Creative
- Footer Mega Grid Columns
- Hero Banner Ultimate
- HTML5 VideoGallery Plus Player
- Meta Slider and Carousel with Lightbox
- Popup Anything on Click
- Portfolio and Projects
- Post Category Image with Grid and Slider
- Post Grid and Filter Ultimate
- Preloader for Website
- Product Categories Designs for WooCommerce
- Responsive WP FAQ with Category (sp-faq)
- SlidersPack – All in One Image Sliders
- SP News And Widget
- Styles for WP PageNavi – Addon
- Ticker Ultimate
- Timeline and History Slider
- Woo Product Slider and Carousel with Category
- WP Blog and Widgets
- WP Featured Content and Slider
- WP Logo Showcase Responsive Slider and Carousel
- WP Responsive Recent Post Slider
- WP Slick Slider and Image Carousel
- WP Team Showcase and Slider
- WP Testimonial with Widget
- WP Trending Post Slider and Widget
How to Check If You're Affected
1. Scan for Essential Plugin plugins
Check your wp-content/plugins/ directory for any of the plugins listed above. Even if you haven't updated recently, you may be running a compromised version.
2. Inspect wp-config.php
Compare your wp-config.php file size against a known-clean backup. In one documented case, the file grew from 3,345 bytes to 9,540 bytes overnight. Look for:
- Large blocks of obfuscated PHP code
- Calls to
analytics.essentialplugin.comor unknown domains - Code that conditionally serves content based on user-agent (especially Googlebot)
3. Check your backup history
If you keep daily backups, compare file sizes across snapshots to pinpoint when the injection occurred. A binary-search approach can help you find the exact window.
4. Monitor outbound connections
The backdoor fetched payloads from analytics.essentialplugin.com. Check your server logs for connections to this domain or any unknown RPC endpoints.
What This Means for Plugin Security
This attack follows the same playbook as the 2017 Display Widgets incident, where a buyer using the alias "Daley Tias" purchased a plugin with 200,000 installs for $15,000 and injected payday loan spam. The difference? This time, it was 30 plugins instead of 9, and the attacker used blockchain-based C2 resolution to evade takedowns.
The hard truth: plugin acquisitions are a known attack vector, and there's no central registry tracking ownership changes. When a plugin changes hands, the new owner has full control over every installation via the WordPress.org update mechanism.
How to Protect Yourself
1. Audit your plugin list
Make a list of every plugin you're running. For each one, ask:
- Who maintains it?
- When was it last updated?
- Has it changed owners recently?
- Does it have a single active maintainer or a team?
2. Prefer plugins with distributed maintenance
Plugins maintained by a team or organization are harder to compromise than those controlled by a single individual who could sell the asset.
3. Monitor plugin changelogs critically
A changelog entry like "Check compatibility with WordPress 6.8.2" shouldn't add 191 lines of code. Treat large, unexplained code additions as red flags.
4. Keep immutable backups
The investigator who uncovered this attack used restic backups with 939 snapshots to trace the exact injection window. If you can't compare against a known-clean state, you're flying blind.
5. Consider patching plugins yourself
In this case, the WordPress.org forced update was a band-aid—it disabled the phone-home mechanism but didn't remove the backdoor module. Some site owners have created patched versions that strip the entire wpos-analytics directory. If you're comfortable maintaining forked plugins, this can be a stopgap until you migrate to alternatives.
The Bigger Picture
This incident exposes a structural weakness in the WordPress ecosystem: plugin ownership is transferable, but trust isn't. When you install a plugin, you're trusting not just the current maintainer, but every future owner who might acquire it.
The WordPress.org Plugins Team has shown it can respond quickly—closing 31 plugins in a single day is impressive. But the response was reactive, not preventive. There's no process for flagging plugins that change ownership, no mandatory security review when SVN access changes hands, and no way for site owners to be notified when a plugin they're using is sold.
Until that changes, the burden falls on us: audit your plugins, monitor your files, and assume that any single-maintainer plugin could be sold to someone with very different intentions.
What to Do Next
If you're running any Essential Plugin plugins:
- Remove them immediately and replace with alternatives
- Scan
wp-config.phpfor injected code - Check your search console for sudden spikes in indexed spam pages
- Review your backup strategy—make sure you can compare against known-clean states
Have you been affected by this attack? Or have you built processes to audit plugin risk in your workflow? Share your thoughts in the comments.
Sources:
Comments